Two critical components of an effective cybersecurity strategy are Vulnerability Assessment and Penetration Testing. While these methodologies share the common goal of fortifying security, their approaches, objectives, and outcomes differ significantly. By understanding Penetration Testing vs Vulnerability Scanning and leveraging the strengths of both, organisations can build a resilient and adaptive security framework.
What is Vulnerability Assessment and Penetration Testing?
Vulnerability Assessment: A Proactive Approach to Risk Identification
A Vulnerability Assessment is an automated and systematic process designed to identify and categorise known weaknesses in an organisation’s systems, networks, and applications. These assessments are preventive, serving as an early warning system to detect vulnerabilities that could be exploited by attackers.
Key Characteristics:
- Automated Scanning: Vulnerability assessments employ advanced tools such as Nessus, Qualys, and OpenVAS to perform detailed scans across a wide range of IT assets, identifying vulnerabilities that could potentially be exploited.
- Broad Coverage: This process covers all critical components of an organisation’s IT infrastructure, including servers, applications, network devices, and databases, ensuring a comprehensive risk overview.
- Risk Prioritisation: Detected vulnerabilities are categorised by severity using standards like Common Vulnerability Scoring System (CVSS). This prioritisation helps organisations focus on remediating the most critical issues first.
- Non-Intrusive Approach: Unlike penetration testing, vulnerability assessments do not exploit detected vulnerabilities. This ensures that systems remain operational during the scanning process, minimising disruption.
Strengths of Vulnerability Assessments
- Comprehensive Coverage: Vulnerability assessments are designed to examine all parts of an IT infrastructure, from servers and network devices to web applications and databases, ensuring that no potential risks are overlooked.
- Speed and Automation: By leveraging automation, these assessments can quickly scan large-scale environments, making them ideal for frequent and consistent security evaluations.
- Risk-Based Prioritisation: Vulnerabilities are categorised based on severity, allowing IT teams to allocate resources effectively and address the most pressing issues first.
- Regulatory Compliance: Vulnerability assessments often fulfill the requirements of compliance standards like ISO 27001, ensuring organizations meet industry and legal obligations.
Limitations:
- Resource-Intensive: Penetration tests require skilled professionals and can be costly and time-consuming, especially for large organizations with complex environments.
- Potential System Impact: Simulated attacks may disrupt business operations if not carefully planned and executed.
- Narrower Scope: Due to budget and time constraints, penetration tests often focus on specific systems or applications, potentially leaving other areas untested.
While vulnerability assessments are efficient for uncovering known vulnerabilities, they may produce false positives and fail to detect zero-day threats or provide context about how vulnerabilities might be exploited.

Penetration Testing: Simulating Real-World Attacks
Penetration testing, often referred to as Ethical Hacking, takes a more aggressive approach by simulating cyberattacks to evaluate the effectiveness of security measures. Unlike Vulnerability Assessments, Penetration Tests actively exploit vulnerabilities to assess their real-world impact and determine the potential damage an attacker could inflict.
Key Characteristics:
- Human Expertise: Conducted by skilled ethical hackers, penetration testing involves real-time decision-making and adaptive strategies that go beyond automated scans.
- Exploit Verification: The process involves simulating actual attacks on identified vulnerabilities to verify their exploitability, providing a clear understanding of the risks involved.
- Scenario-Based Testing: Tests can be tailored to specific organizational concerns, such as simulating phishing attacks, ransomware breaches, or insider threats to evaluate preparedness.
- Contextual Insights: Pen testers often highlight how multiple vulnerabilities could be chained together, revealing complex attack paths that automated tools might miss.
Strengths of Penetration Testing
- Real-World Risk Validation: Penetration testing mimics actual attack scenarios, providing a realistic understanding of how vulnerabilities could be exploited and the damage that could result.
- Tailored Testing: Each test is customized to an organization’s specific risk landscape, focusing on high-value assets and potential attack vectors.
- Actionable Insights: Testers deliver comprehensive reports that not only identify weaknesses but also provide practical recommendations for mitigation.
- Enhanced Awareness: By demonstrating how attackers could breach defenses, penetration testing helps organizations build stronger security measures and improve overall preparedness.
Limitations:
- Resource-Intensive: Penetration tests require skilled professionals and can be costly and time-consuming, especially for large organizations with complex environments.
- Potential System Impact: Simulated attacks may disrupt business operations if not carefully planned and executed.
- Narrower Scope: Due to budget and time constraints, penetration tests often focus on specific systems or applications, potentially leaving other areas untested.
Although penetration testing delivers deep insights, it is resource-intensive, costly, and may disrupt systems if not carefully managed.

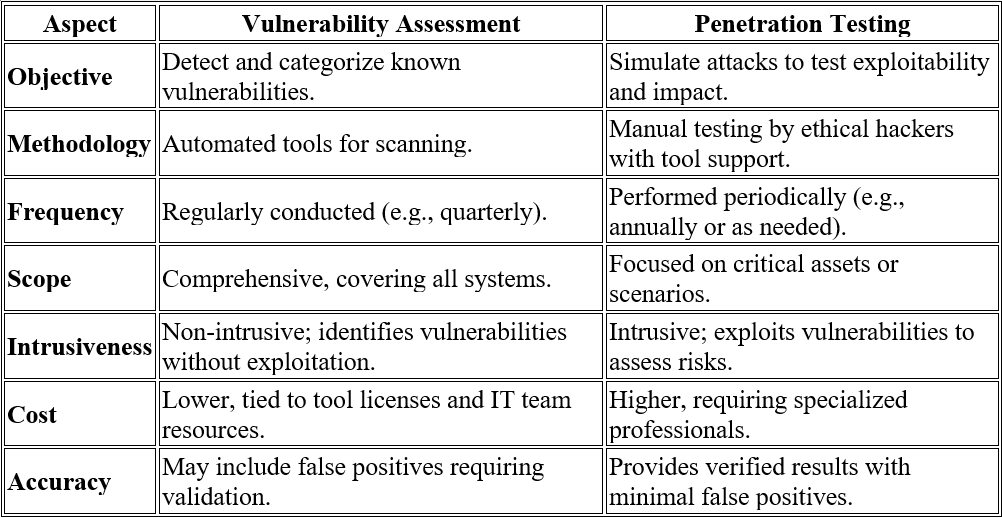
Comparing Vulnerability Assessment vs Penetration Testing
The Need for Integration
Integrating vulnerability assessments and penetration testing creates a balanced cybersecurity approach that leverages the strengths of both methodologies.
- Comprehensive Risk Identification: Vulnerability assessments provide a broad overview of potential weaknesses, while penetration testing dives deeper to validate and explore the real-world implications of those weaknesses.
- Proactive and Reactive Defenses: Vulnerability assessments enable organizations to proactively address known vulnerabilities, while penetration testing ensures that defenses can withstand real-world attacks.
- Enhanced Resource Allocation: Combining the results of both assessments allows IT teams to prioritize remediation efforts more effectively, addressing critical vulnerabilities first while planning long-term security improvements.
- Continuous Improvement: Regularly integrating both practices ensures organizations remain resilient against evolving threats and adapt to new attack vectors.
Industry Trends and Supporting Statistics
The cybersecurity landscape is rapidly evolving, with rising threats emphasizing the need for robust security measures. Key trends and statistics underline the importance of vulnerability assessments and penetration testing in maintaining a strong defense.
- Global Cybercrime Costs: Cybercrime is projected to cost $10.5 trillion annually by 2025 (Cybersecurity Ventures). This highlights the critical need for proactive security practices to avoid financial losses, operational disruptions, and reputational harm.
- Small Business Vulnerability: With 43% of cyberattacks targeting small businesses, regular vulnerability assessments and penetration testing provide affordable, effective defenses for organizations with limited resources.
- Zero-Day Vulnerabilities: Zero-day attacks have risen by 125% (MITRE). While vulnerability scans may miss these threats, penetration testing offers hands-on strategies to detect and mitigate unknown risks.
- Cost of Data Breaches: Data breaches average $4.45 million in costs (IBM), making preemptive investments in security testing essential to prevent costly legal fees, downtime, and reputational damage.
Practical Applications of Security Testing
- Financial Institutions: Regular vulnerability scans and penetration testing ensure compliance with PCI DSS, safeguarding payment systems and online platforms against phishing and ransomware.
- Healthcare Providers: Vulnerability assessments and penetration testing help secure patient data, address risks in medical devices, and enhance responses to threats like ransomware while meeting NHS requirements.
- E-Commerce Platforms: Combining assessments and testing protects customer data, ensures secure transactions, and reduces downtime during incidents, boosting customer confidence and operational reliability.
Vulnerability management and Penetration testing are indispensable tools for organisations across industries, providing proactive measures to combat today’s complex cyber threats.
Contact Creative Networks Today
At Creative Networks, we offer tailored cybersecurity solutions to meet your organization’s specific needs. Whether it’s conducting Penetration testing to simulate real-world attacks or performing Vulnerability Management to identify weaknesses, our expert team is here to ensure your digital assets are fully protected.
Let us help you proactively safeguard your business against evolving cyber threats.
Contact Creative Networks today to schedule a penetration test or Vulnerability management or explore our full range of cybersecurity services. Together, we’ll build a robust security framework for your organization.




